With escalating cyber threats, embedding security into the software development life cycle is no longer a technical nicety but a strategic imperative. Organisations that prioritise secure by design principles not only mitigate risk but also gain a competitive edge through enhanced customer trust, regulatory compliance, and accelerated development cycles.
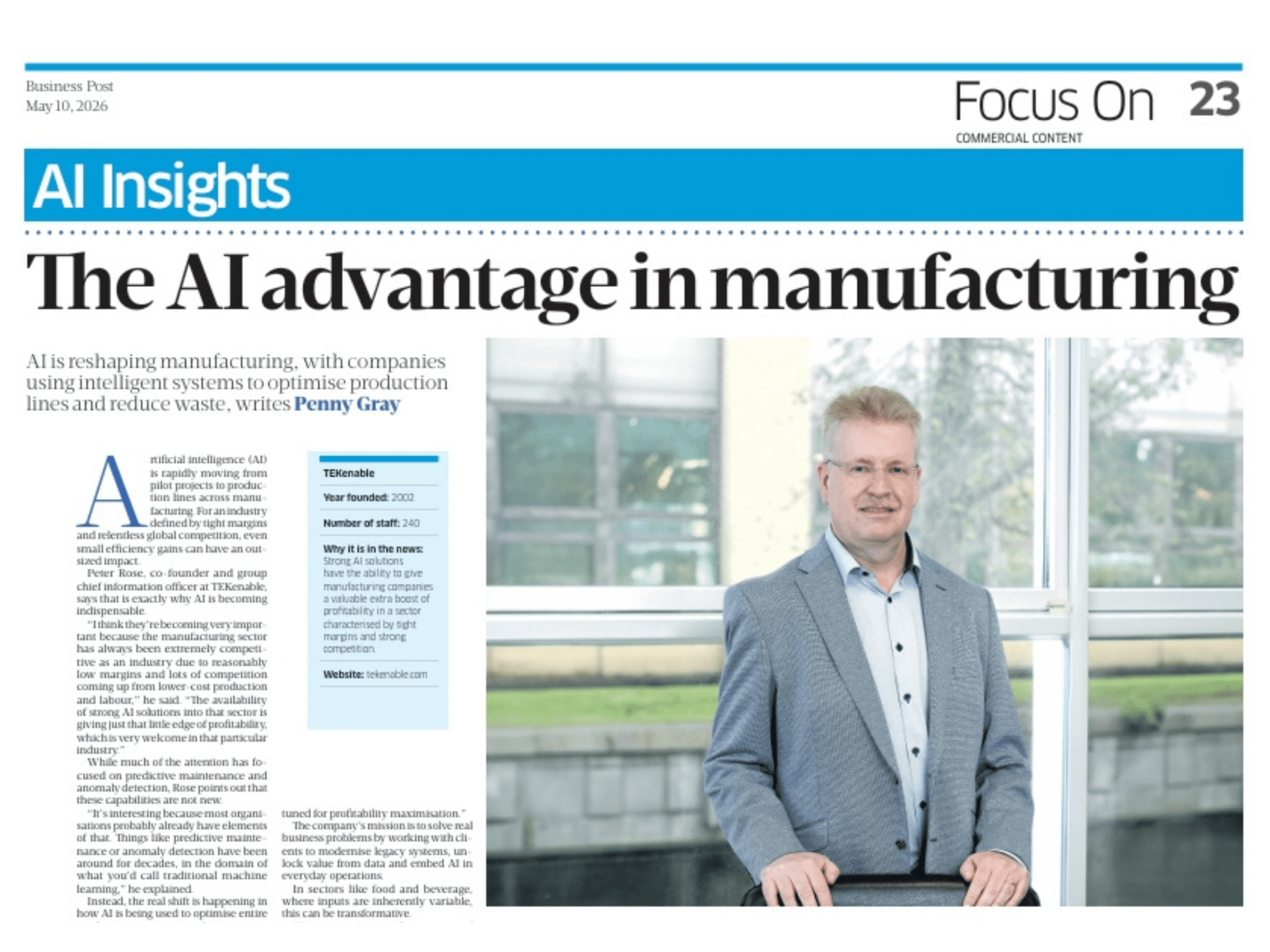
Peter Rose, Group Chief Technical Director, TEKenable
Today’s cybersecurity environment presents unprecedented challenges for organisations across all sectors, private and public alike. Cyber attacks are growing not just in frequency, but in sophistication and impact. According to Fortinet research, some 68% of organisations face elevated risks due to a critical shortage of trained security personnel, coinciding with the rise of AI-supported attacks.
What many business leaders fail to recognise is that no organisation is immune. Traditional security approaches focusing primarily on network protection have proven woefully inadequate in this new reality where attackers specifically target weaknesses in application code, development processes and individuals.
The cost of insecure software
The financial implications of software vulnerabilities extend far beyond immediate remediation costs. Data breaches resulting from insecure software can devastate an organisation’s bottom line through regulatory penalties, legal liabilities, operational disruptions, and emergency patching exercises.
Perhaps most concerning is the escalating cost of addressing security issues after deployment. Research consistently shows that fixing security vulnerabilities during production costs many times more than addressing the same issues during the design phase. This “technical debt” accumulates interest rapidly in the form of emergency patches, unplanned downtime, and diverted development resources.
The secure by design approach
The “secure by design” philosophy represents a fundamental shift in how organisations approach software development. Rather than treating security as a separate consideration addressed primarily through testing and patching, this approach integrates security principles throughout the entire Software Development Life Cycle (SDLC).
From initial concept through requirements gathering, design, development, testing, deployment, and maintenance, security considerations inform every decision. This proactive stance stands in stark contrast to the traditional “bolt-on” approach, where security assessments occur primarily at the end of development. By shifting security “left” in the development timeline, organisations prevent vulnerabilities rather than merely detecting them.
Secure coding practices and technologies
To implement secure-by-design effectively, developers must adopt specific secure coding practices and leverage appropriate technologies. Secure coding practices involve writing code that minimises vulnerabilities by adhering to well-established principles including input validation (to prevent injection attacks), proper error handling (to avoid information leakage), and the principle of least privilege.
A range of technologies supports these practices. Static Application Security Testing (SAST) tools analyse source code to identify potential vulnerabilities early, while Dynamic Application Security Testing (DAST) tools examine the running application. Interactive Application Security Testing (IAST) combines elements of both for more comprehensive analysis. Furthermore, robust authentication frameworks, encryption libraries, and secure configuration management tools are essential components of a secure development environment.
The benefits of secure by design
Economic and operational advantages
The economic case for secure by design is compelling. By preventing vulnerabilities early in development, organisations dramatically reduce costs associated with emergency patches, incident response activities, breach notification, extended maintenance of vulnerable systems, and regulatory penalties.
Contrary to the misconception that security slows development, mature secure-by-design practices actually accelerate delivery timelines. By preventing security-related rework and production emergencies, development teams maintain momentum and focus on value-adding features rather than reactive fixes. When security issues emerge late in development or after release, they create unpredictable delays and disrupt release schedules. To support this approach effectively, many companies choose to hire dedicated developers who can focus on building security into every stage of the project.
Trust, compliance and competitive edge
In an age of heightened privacy concerns, software security has become a key differentiator in customer perception. Organisations demonstrating a comprehensive approach to protecting sensitive data build stronger relationships with increasingly security-conscious customers.
The regulatory landscape for data protection continues to expand with frameworks like the EU’s GDPR, the Health Insurance Portability and Accountability Act (HIPPA) in the US, and the Payment Card Industry Data Security Standard (PCI DSS), as well as industry-specific requirements. Secure-by-design practices align naturally with these compliance requirements, reducing the friction between innovation and regulatory adherence. Rather than treating compliance as a separate workstream that constrains development, organisations embedding security throughout the SDLC find that compliance becomes an organic outcome of their development process.
Market effects
Most significantly, secure software development practices increasingly represent a key market differentiator. Organisations demonstrating mature security practices gain advantages in winning security-conscious enterprise customers, entering regulated markets, maintaining customer loyalty in the face of industry breaches, attracting partners seeking to minimise supply chain risks, and reducing insurance premiums tied to cyber risk.
Overall, the transition to cloud platforms offers significant opportunities to enhance security when approached thoughtfully. Cloud environments provide centralised information assets with consistent security controls, improved security posture compared to unpatched on-premise systems, and rich security services that can be integrated into development pipelines.
Modern cloud platforms provide robust tooling for secure DevOps Tools practices, continuous security testing, and automated vulnerability management. These capabilities, when leveraged properly, enable organisations to implement secure-by-design principles at scale without sacrificing agility.
Addressing the skills gap challenge
The security talent shortage represents one of the most persistent challenges to implementing secure development practices. With 68% of organisations reporting that the skills gap increases their risk exposure, building security capacity requires creative approaches:
- Training developers in secure coding practices rather than relying exclusively on security specialists
- Fostering a security-first culture where everyone shares responsibility for security outcomes
- Leveraging automation to compensate for human resource limitations
- Implementing security champions programmes within development teams
- Partnering with specialised security service providers, for example a Ruby on Rails staff augmentation company, to augment internal capabilities
The AI-powered threat evolution
The emergence of AI-enhanced attack methodologies creates new challenges for secure development. Adversaries now leverage machine learning to craft highly personalised phishing campaigns, identify and exploit vulnerabilities at unprecedented speed, generate malware variants that bypass signature-based defences, and automate complex attacks previously requiring human expertise.
This evolution demands corresponding advancements in defensive strategies. Forward-thinking organisations are countering these threats by incorporating AI into their own security practices, using machine learning for anomaly detection, behavioural analysis, and automated threat response. They work on the assumption that phishing has been successfully undertaken by the bad actors while working to reduce the instances in which it is successful and the impact that it has.
TEKenable’s approach to secure software development
TEKenable embraces a security-first approach to software development that permeates every aspect of our delivery methodology. As Peter Rose, our security lead, emphasises: “Security cannot be an afterthought in modern software development. It must be woven into the fabric of how we design, build, and maintain applications.”
Our secure development process integrates:
- Comprehensive threat modelling in the design phase to identify and mitigate potential vulnerabilities
- Secure coding standards enforced through automated code analysis
- Regular security testing throughout development using both automated tools and manual techniques
- Continuous security monitoring in production environments
- Regular security training for all development personnel
In addition, our expertise in AI software development provides unique insights into both emerging threats and defensive capabilities. We leverage this knowledge to help clients not only build secure applications today but prepare for tomorrow’s security challenges.
TEKenable’s consultative approach begins with helping businesses understand their security posture holistically. Rather than focusing solely on technical controls, we work with clients to develop comprehensive strategies that align security practices with business objectives, regulatory requirements, and risk tolerance.
Conclusion: security before ‘cyber’
In today’s threat landscape, secure software development isn’t merely a technical requirement but a business imperative with far-reaching implications for competitive positioning. Organisations that successfully embed security throughout their development lifecycle transform what could be a liability into a powerful market advantage.
By preventing costly vulnerabilities rather than addressing them after deployment, these security-conscious organisations reduce costs, accelerate delivery, build customer trust, maintain regulatory compliance, and differentiate themselves in increasingly security-conscious markets.
The choice is clear: embrace secure-by-design principles to not only protect digital assets but create lasting competitive advantage.
Contact TEKenable today for a consultation on secure software development practices or a security assessment of your existing applications. Let us help you transform security from a necessary cost into a strategic advantage.
Secure Software Development FAQs:
What does “secure by design” mean in software development?
It means embedding security principles throughout the entire Software Development Life Cycle (SDLC), from planning and design to deployment and maintenance, rather than adding security as an afterthought.
Why is it important to address security early in the development process?
Fixing vulnerabilities during production is significantly more expensive and disruptive than addressing them during design. Early security integration reduces technical debt and emergency fixes.
What are some key secure coding practices developers should follow?
Practices include input validation, proper error handling, using the principle of least privilege, and avoiding hard-coded credentials. These help prevent common vulnerabilities like injection attacks and data leaks.
Which tools support secure software development?
Tools like Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), and Interactive Application Security Testing (IAST) help identify and fix vulnerabilities. Secure configuration management and encryption libraries are also essential.
How does secure-by-design help with regulatory compliance?
By embedding security throughout the SDLC, organisations naturally align with frameworks like GDPR, HIPAA, and PCI DSS, making compliance smoother and more sustainable.
What can organisations do to overcome the cybersecurity skills gap?
They can train developers in secure coding, foster a security-first culture, automate security tasks, implement security champions programmes, and partner with specialised security providers.