Information security tends to focus on protecting the network, but we must take a security-first approach to software development and deployment too
Every organisation today knows that the threat from cyber criminals is neither exaggerated nor something that is for other people to worry about. And yet, the reality today is that many businesses remain unprepared for it – and this is despite the fact that being in business today means being online.
Naturally, the ongoing information security skills shortage has not helped: 68 per cent of organisations surveyed by security vendor Fortinet in 2023 said they faced additional risks due to a lack of trained personnel.
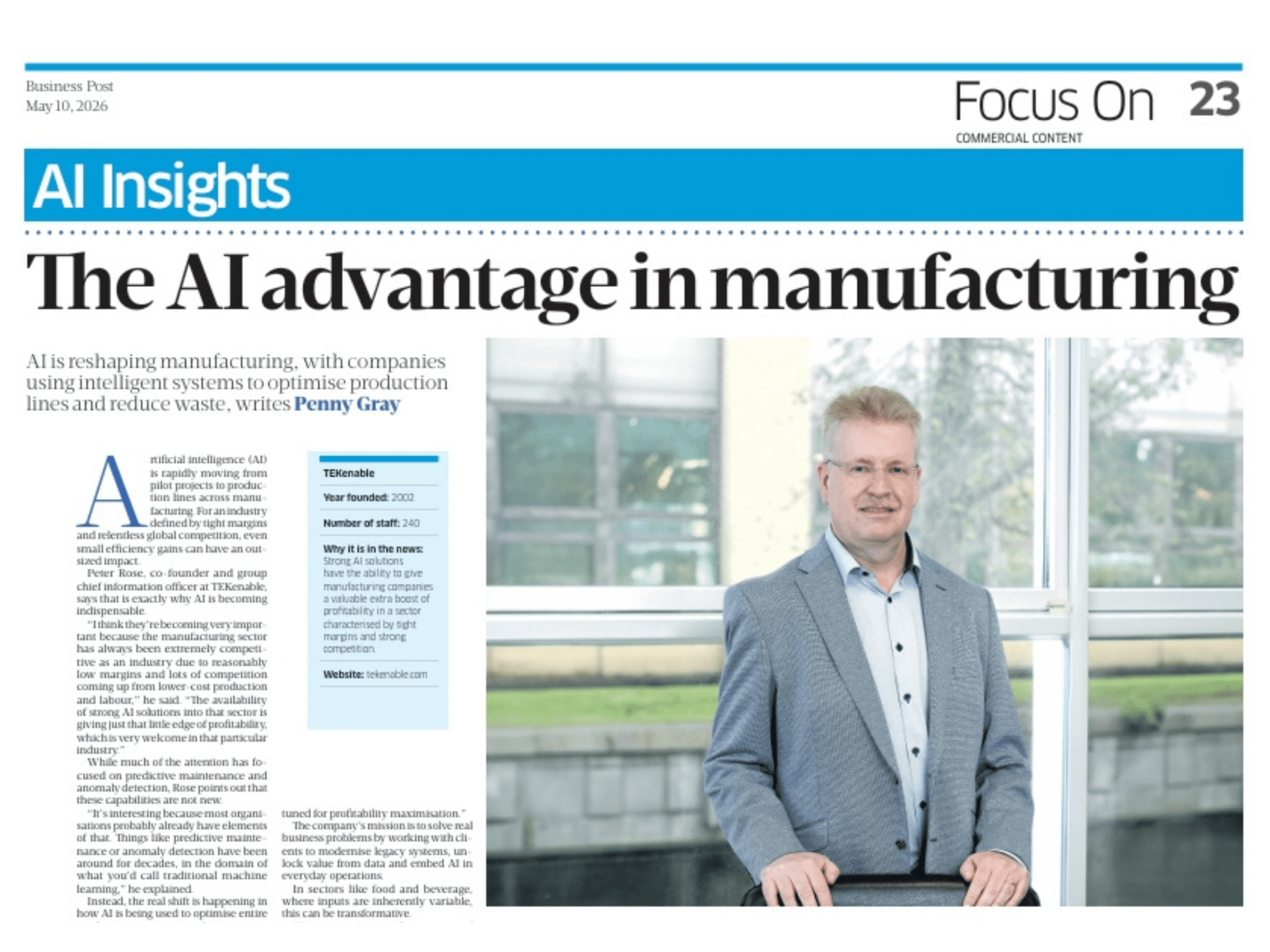
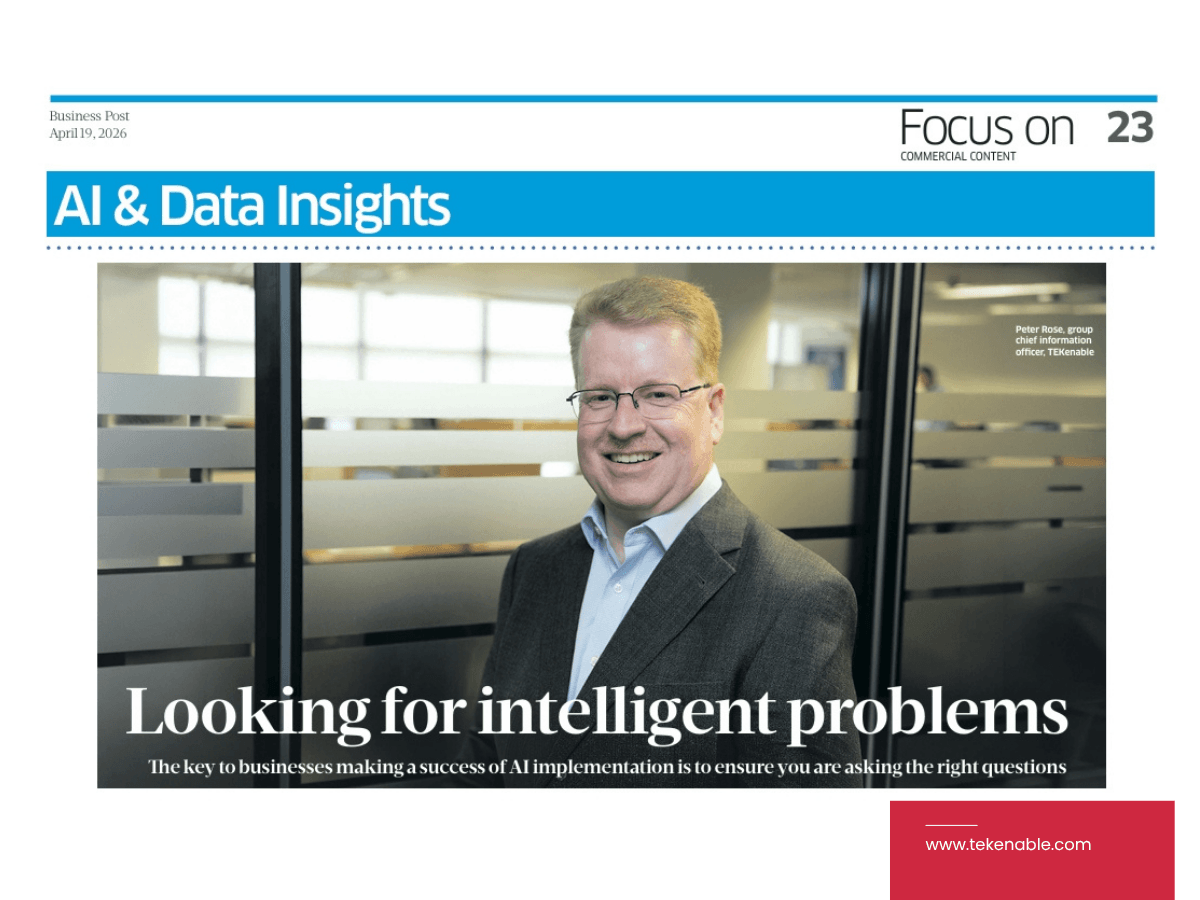
“It’s really bad. However, press coverage of high-profile incidents has driven demand for skills,” said Peter Rose, group chief technology officer at TEKenable.
As a developer working with businesses to bring about digital transformation, including developing custom software solutions, TEKenable has taken a security-first approach to all of the software it develops and deploys.
The move toward cloud computing has had a positive impact, Rose said, firstly by centralising information assets, but also because cloud is simply more secure than on-premise systems, which are often left unpatched and may not have been designed for contemporary practices such as remote access.
“It [cloud] has helped by enabling a core standard set of skills to be applicable to a wide range of clients rather than having to learn specific products and services for each customer. Business skills are not affected by cloud; the capability to make a risk assessment, design suitable controls and present progress to a board are the same,” he said.
Identifying risk
The single most common type of attack today is ‘phishing’, a type of social engineering attack that uses fraudulent emails or text messages to trick victims into revealing personal information or clicking on malicious links. Indeed, as of 2023 Google alone is now blocking around 100 million phishing emails daily. To reduce the risk of falling victim, paying attention to email security can help identify suspicious messages before they cause harm.
This picture is supported by further research conducted by the FBI’s Internet Crime Complaint Center (IC3), whose most recent Internet Crime Report found that phishing was the most prevalent threat in the US, with 323,972 victims – up 34 per cent compared to the previous year.
However, there is a new aspect to phishing, Rose said.
Overall, the ‘threat surface’, meaning the areas where an organisation can be attacked, are enormous, and while the network itself tends to get at least some attention, what can be forgotten about is that attacks can come via vulnerabilities in software and even fairly innocuous-seeming hardware solutions.
“Third-party suppliers remain a potential soft underbelly – for example, the recent Met Police leak from their ID card printers, and then you have insider risk, deliberate or inadvertent, as shown by the recent PSNI data breach,” Rose said.
Although total security cannot ever be guaranteed, Rose said that the right way to start is by understanding what you actually have, including not only your network but also your people and any custom software. From there, a comprehensive strategy can be developed.
“You start by identifying assets, be that data, intellectual property, staff, or property, and assess the risks to these,” he said.
“Businesses need to assess the probability of an attack and calculate the potential impact per asset, and then risk and rank accordingly. Starting with the highest rank, first you either accept the risk or else develop controls to mitigate it until an acceptable level of risk has been achieved. Then you can consider budget constraints, which will inform what can be done.”
Notably, artificial intelligence (AI)-supported attacks are on the rise. Alarming as this is, it is not surprising: any new and useful technology will be adopted by criminals in search of gains.
“Phishing is still the biggest threat, but it is now helped by generative AI crafting the messages. AI-supported attack analysis and AI-generated attacks have become a reality,” said Rose.
Indeed, a recent report in Wired magazine revealed that criminals have created their own ChatGPT clones and are now touting large language models (LLMs) for phishing or creating malware.
However, AI could be the answer to AI-assisted attacks, Rose said.
TEKenable, which is itself an AI software developer, has a deep and broad view of the current state of the technology and where it is likely to go.
“In my view, humans will need to step out of the loop here. An AI can attack and breach faster than a human defender can analyse what is happening and defend. As a result, AI will need to defend in fully automatic mode, not just as a supportive technology,” Rose said.
In a sense, then, the deployment of AI as both attack and defence is simply the latest salvo in an unending war between criminals and their targeted victims. What matters, therefore, is that businesses remain alert and take security seriously across their entire organisation.
“It does lead to an arms race between AI attacker and AI defender. The player with the best algorithms, largest training data and biggest budget wins – and wins globally,” said Rose.