Remote working is about more than replicating the office in a spare room. Instead, it requires a rethink of the technologies used in an organisation and the processes and procedures.
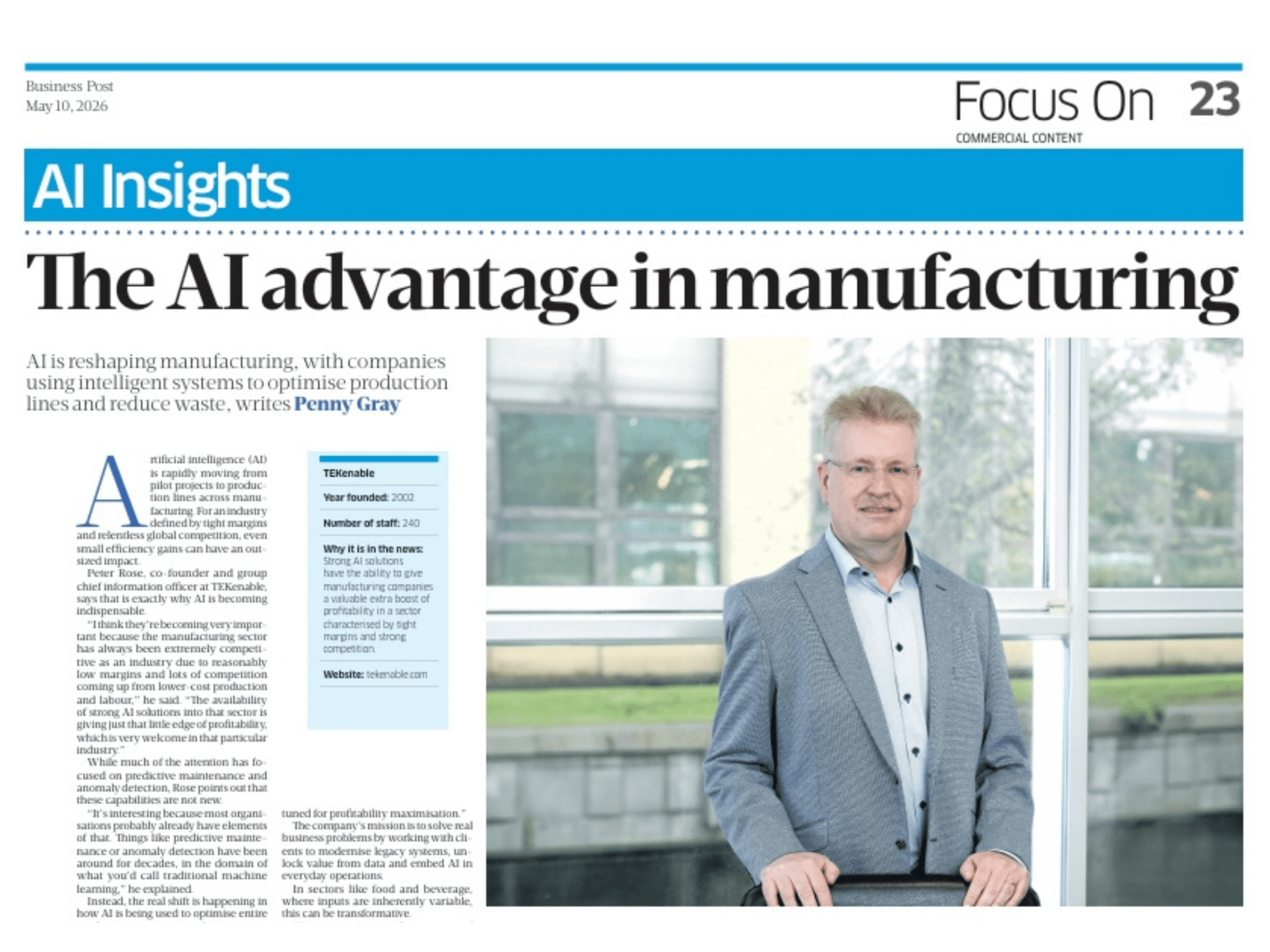
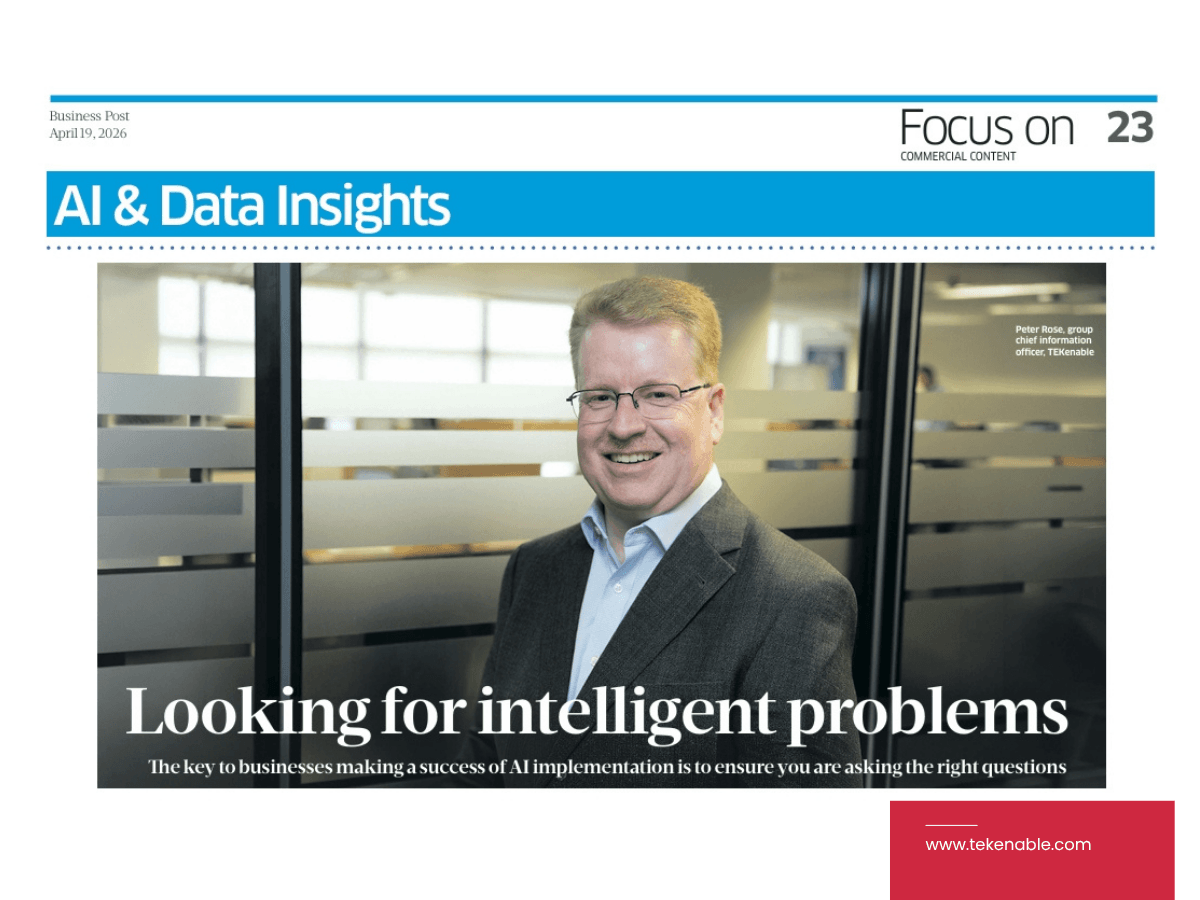
Peter Rose, Group Chief Technical Director, TEKenable
To say that the workplace has changed in recent years is something of an understatement, with the biggest change being an increase in hybrid and remote working.
Indeed, according to the Remote Working in Ireland survey conducted by the Western Development Commission and the University of Galway, 59 per cent of respondents were now working hybrid (sometimes remotely, sometimes on site) and 38 per cent were working fully remotely.
Naturally, this means organisations have had to adapt.
Peter Rose, group chief technical director of TEKenable, which is itself now a remote-first organisation, said that remote working is overall very beneficial, but it does raise new issues. Chief amongst them is security, which has to be approached differently, and not just in terms of technological solutions.
“In my view remote work tends to increase trust in electronic communications and may therefore make people a little more susceptible to deception,” he said.
In fact, this is borne out by recent invoice redirection scams, including a recent case in Hong Kong that saw an employee of a multinational pay a bogus invoice for $200 million Hong Kong dollars (approx. €23.5 million). Astonishingly, the employee was concerned about the invoice and so scheduled a conference call to check if it should be paid but was confronted by convincing ‘deep fakes’ of his bosses on the call.
It is not necessary to imagine such dramatic cases, however, simply to understand that remote working can pose risks and therefore demands a new approach.
“The lack of physically close colleagues to verify things with and the normality of almost all communications being electronic feeds a higher level of trust that has to be countered with a higher level of training and testing,” Rose said.
In addition, a move to remote working is the final nail in the coffin of already outmoded perimeter-focussed security. After all, there is no point in digging a moat and filling it with crocodiles if there is no-one inside the castle.
Remote work tends to increase trust and may therefore make people a little more susceptible to deception
“Clean desk policy is impossible to enforce [in a remote working scenario] and you do not control the LAN in which the employee’s laptop is operating, nor the other devices that it is exposed to as a result, or the wifi, or physical firewall,” said Rose.
What can be done, though, is very precise management of devices.
“Remote working can create a very high degree of micro-segmentation in which no end point device can see any other endpoint device, making lateral movement very hard indeed compared to a flat LAN in an office,” he said.
Cloud, of course, helps, as it means infrastructure can be removed from the picture altogether. TEKenable, for its part, has no systems in any of its offices other than wifi and an internet connection.
“Everything else is cloud-based,” Rose said.
One question many remote workers will have is: is it possible to reduce or otherwise rationalise the blizzard of documents, e-mails and instant messages that come with working out of the office.
The answer, Rose said, is not straightforward, as communication and collaboration are still required.
“It’s very hard, but Microsoft CoPilot really helps. I can ask it to summarise all unread emails from the past n days and show them to me as bullet points. I can then decide which to respond to and tell CoPilot what I want to say in reply, which is much quicker but no less effective than reading the emails,” he said.
Indeed, a similar approach can be taken with large documents, and this is perhaps the key to the modern workplace: work smarter, not harder.
“I ask CoPilot to summarise the key ideas and then read the parts that are relevant only,” Rose said.
The above text was reproduced from the interview published in BusinessPost on April 12th, 2024.